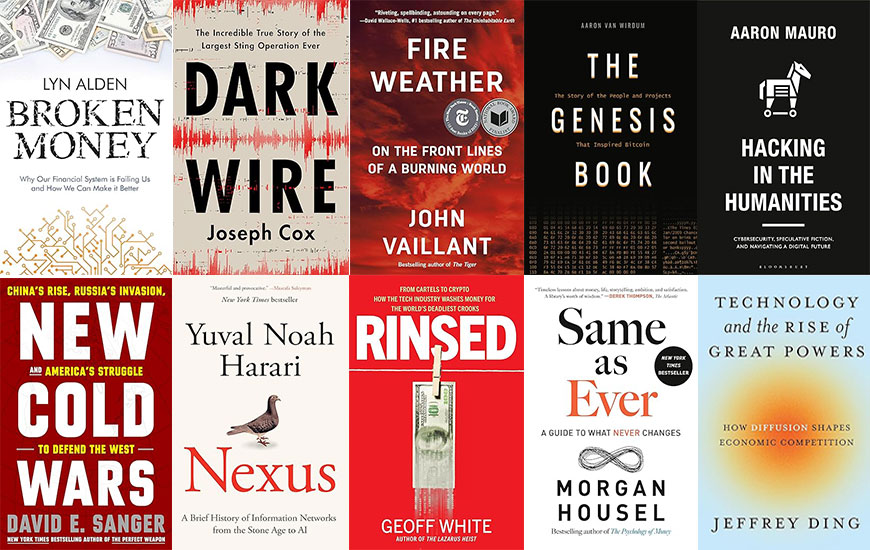
Top 10 Security, Technology and Business Books of 2024
Welcome to 8th edition of my annual top 10 books list! Each year, I read close to 100 books and distill down my 10 favorite security, technology and business books into this top 10 list and also include my favorite fiction books of year and a…
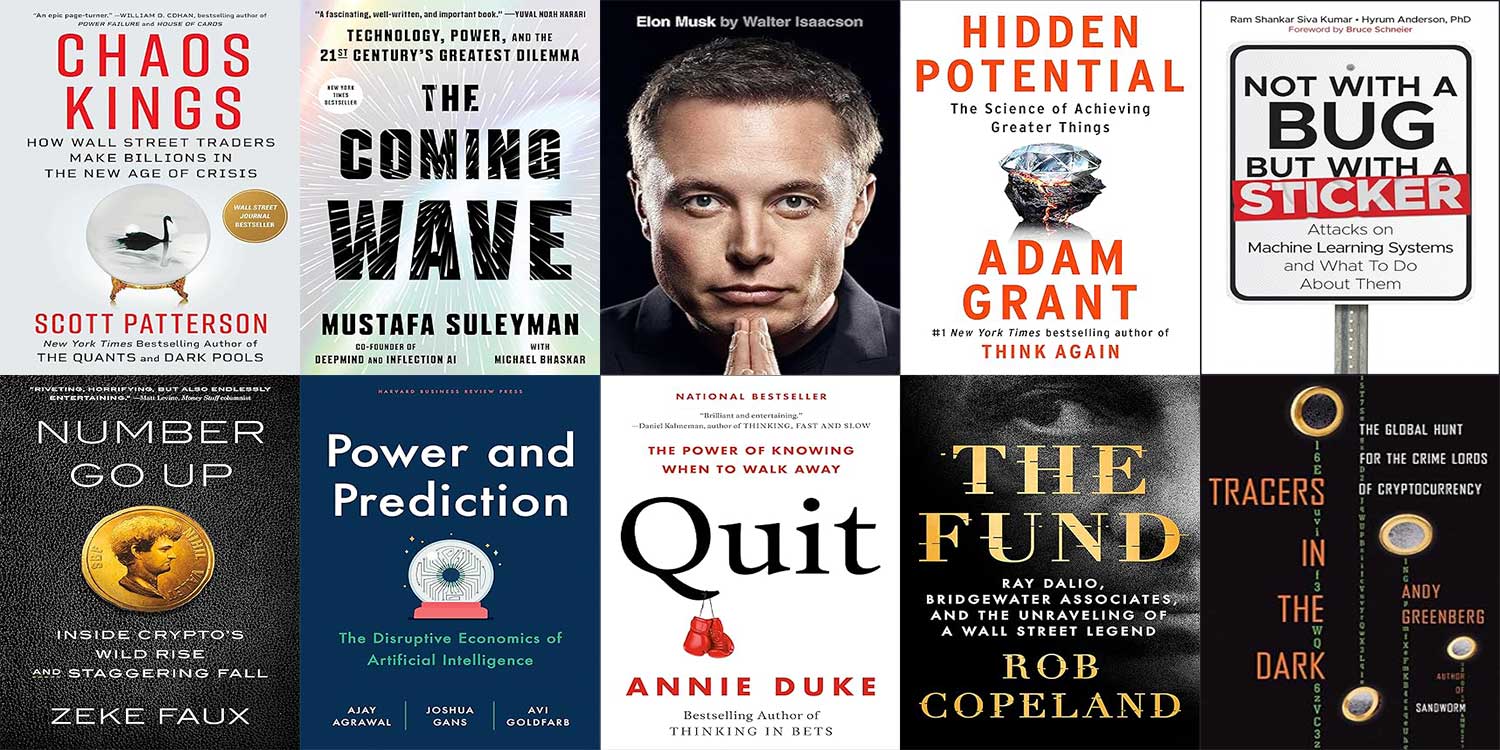
Top 10 Security, Technology, and Business Books of 2023
The year 2023 felt incredibly disruptive and my annual reading list probably reflects that fact as I sought out books that focused not only on managing risk and chaos, but recognizing and fostering disruptive technology opportunties. Five years ago,…
My Top 10 Security, Technology and Business books of 2022
Head on over to OODAloop.com for my top 10 books of 2022. https://www.oodaloop.com/archive/2022/11/23/top-10-security-technology-and-business-books-of-2022/
Happy 25th Anniversary to the Terrorism Research Center
Today marks the 25th anniversary since the founding of the Terrorism Research Center. I think I captured the continuing legacy of the TRC well in my 20th anniversary note, so sharing below for broader distribution. Twenty years. If you had told me…
Most Popular Posts of 2019
I publish most of my content at OODAloop.com these days, but thought I'd document for the blog, the most popular pieces of content from 2019. The Third Decade Problems Deception Needs to be an Essential Element of Your Cyber Defense Strategy A…
Top 10 Security, Technology and Business Books of 2019
My annual compilation of best books for the year 2019 is now live at OODA Loop. I read over 100 books to select the ten best of the year. Also, please consider subscribing to my weekly email newsletter that tracks the top cyber and technology…
The Third Decade Problems
Meaningful work is the opus of a successful career and over the past two decades, I’ve had the humbling honor of working impactfully on important issues. In the early and mid-90’s, I helped identify the next generation of conflict in the…
Top 10 Security, Technology and Business Books of 2018
My annual compilation of top books is up over at OODA Loop. Enjoy. Top 10 Security Technology and Business Books of 2018 - OODA
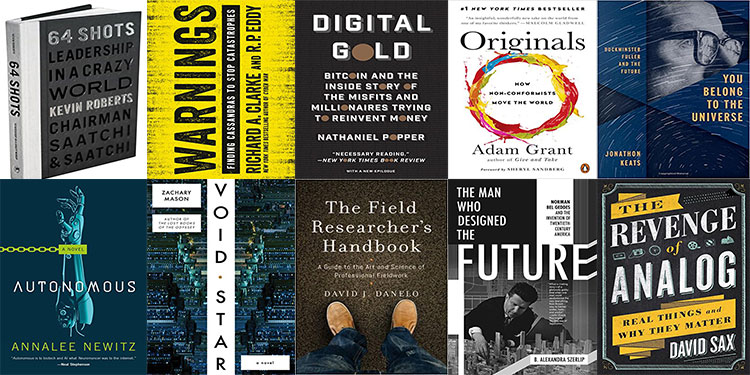
Top 10 Security, Business, and Technology books of 2017
I've compiled my annual list of top books. Not your typical top ten list. Check it out at OODA Loop
Best Security, Business, and Technology Books of 2016
"Dozens of times per year, I get asked to recommend my favorite books so I couldn’t say no when the OODA Loop team asked me to build on Mark Mateski’s popular Red Teaming book list by providing my top 10 books for 2016. I have very eclectic…